This post will explain Best penetration testing tools. The idea behind penetration testing is to determine security-related vulnerabilities in a software application. Also called pen testing, the specialists who perform this testing are called ethical hackers who identify the activities conducted by criminal or black hat hackers.
Penetration testing aims in avoiding security attacks by carrying out a security attack to understand what damage can a hacker cause if a security breach is attempted, the outcomes of such practices helps in making the applications and software more safe and potent.
Top 16 Best Penetration Testing Tools in 2022
In this article, you can know about Best penetration testing tools here are the details below;
So, if you utilize any software application for your business, a pen-testing method will help you inspect the network security hazards. To carry forward this movement, we bring to you this list of the best penetration testing tools of 2022!
1. Acunetix.
An entirely automated web scanner, Acunetix look for vulnerabilities by determining above 4500 web-based application threats which likewise consists of XSS and SQL injections. This tool works by automating the jobs which may take several hours if done by hand to provide preferable and steady results.
This threat detection tool sustains javascript, HTML5, and single-page applications consisting of CMS systems, and gets advanced handbook tools related to WAFs and Issue Trackers for pen testers.

Acunetix Web Application Security Scanner.
2. Netsparker.
Netsparker is another automated scanner readily available for Windows and an online service that discovers hazards associated with Cross site Scripting & SQL Injections in web applications and APIs. Also check Tools and resources for designers and agencies
This tool checks for susceptibilities to prove as if they are genuine and not false positives so that you don’t need to invest long hours inspecting vulnerabilities by hand.

Netsparker Web Application Security.
3. Hackerone.
To find and repair the most delicate dangers, there is nothing that can beat this leading security tool “Hackerone”. This quick and effective tool operates on the hacker-powered platform that immediately offers a report if any risk is discovered.
It opens the channel to let you connect with your group straight with tools like Slack while using interaction with Jira and GitHub to let you associate with advancement teams.
This tool features observation standards such as ISO, SOC2, HITRUST, PCI, & so on without any extra re-testing cost.
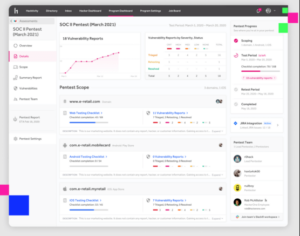
Hackerone Security and Bug Bounty Platform.
4. Core Impact.
Core Impact has an outstanding series of exploits in the market which permits you to carry out the complimentary Metasploit exploits within the structure.
With an capability to automate the processes with wizards, they feature an audit path for PowerShell commands to re-test the clients by simply replaying the audit.
Core Impact reports its own Commercial Grade exploits to supply superior quality with technical assistance for their platform and exploits.
CoreImpact Penetration Testing Software Application.
5. Intruder.
Trespasser offers the very best and the most workable way to discover vulnerabilities associated with cybersecurity while discussing the dangers and helping out with the solutions to cut off the breach. This automatic tool is for penetration testing and homes more than 8999 security checks.
The security assessments of this tool feature missing spots, common web app issues like SQN Injections, & misconfigurations. This tool also aligns the products on the basis of context & thoroughly scans your systems for hazards.
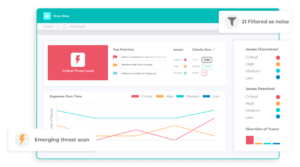
Intruder Vulnerability Scanner.
6. Breachlock.
Breachlock or RATA web application threat detection scanner is an AI or expert system, cloud, and human hacking-based automatic scanner that needs unique skills or expertise or any setup of hardware or software application.
The scanner opens with a number of clicks to check for vulnerabilities and informs you with a report of findings with recommended solutions to get rid of the problem. This tool can be combined with JIRA, Trello, Jenkins, and Slack and offers real-time outcomes without false positives. Also check Linux tools for digital artists

Breachlock Penetration Testing Service.
7. Indusface Was.
Indusface Was i for manual penetration testing combined with its automated vulnerability scanner for detection and reporting of prospective threats on the basis of OWASP vehicle including site track record links examine, malware check, and defacement examine the website.
Anyone carrying out manual PT will immediately receive an automatic scanner which can be utilized on-demand for the whole year. Some of its functions include:.
– Pause and resume.
– Scan single-page applications.
– Endless proof of idea demands to supply noted evidence.
– Scanning for malware infections, defacement, broken links, and track record of links.
– Throughout assistances for talking about POC and removal standards.
– Free trial for a thorough single scan with no charge card information.

IndusfaceWAS Web Application Scanning.
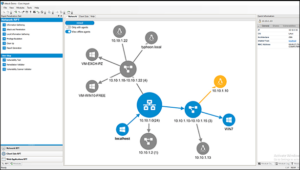
8. Metasploit.
Metasploit a sophisticated and desired structure for penetration testing is based upon a make use of that consists of a code that can pass through the security standards to intrude any system. On intruding, it performs a payload to perform operations on the target maker to create a perfect structure for pen-testing.
This tool can be utilized for networks, web applications, servers, and so on plus, it features GUI clickable user interface and command line that works with Windows, Mac, and Linux.
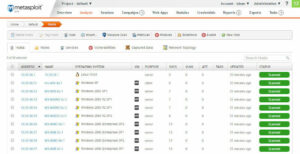
Metasploit Penetration Testing Software Application.
9. w3af.
w3af web app attack & audit framework are housed with web integrations & proxy servers in codes, HTTP requests, & injecting payloads into various sorts of HTTP requests, & so on. The w3af is equipped with a command line interface that performs for Windows, Linux, & macOS.
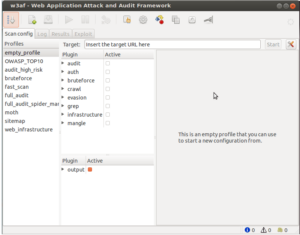
w3af Application Security Scanner.
10. Wireshark.
Wireshark is a favored network protocol analyzer that provides every minor detail related to packet information, network procedure, decryption, etc.
Appropriate for Windows, Solaris, NetBSD, OS X, Linux, & more, it fetches data using Wireshark which can be witnessed via TTY mode TShark utility or GUI.
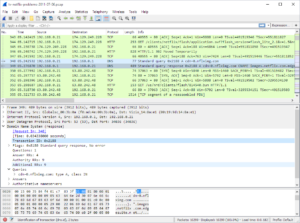
Wireshark Network Package Analyzer.
11. Nessus.
Nessus is one of the robust and outstanding threat detection scanners that expertise in delicate data search, compliance checks, site scanning, and so on to identify the weak points. Compatible for multi-environments, it is among the best tools to select. Also check sales productivity tools
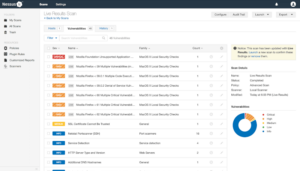
Nessus Vulnerability Scanner.
12. Kali Linux.
Managed by Offensive Security, Kali Linux is an open-source Linux circulation that includes complete modification of Kali ISOs, Ease Of Access, Full Disk File Encryption, Live USB with Multiple Determination Stores, Android Compatibility, Disk Encryption on Raspberry Pi2, and more.
Besides, it also features a few of the pen testing tools like Tools noting, variation tracking, & Metapackages, etc, making it an flawless tool.

Kali Linux.
13. OWASP ZAP Zed Attack Proxy.
Zap is a free pen testing tool that scans for security vulnerabilities on web applications. It uses numerous scanners, spiders, proxy intercepting aspects, etc to learn the possible hazards. Ideal for the majority of platforms, this tool will not let you down.
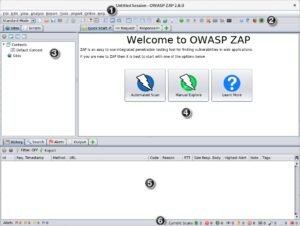
OWASP ZAP Application Security Scanner.
14. Sqlmap.
Sqlmap is another open source penetration testing tool that can not be missed. It is mainly utilized for identifying and making use of SQL injection problems in applications and hacking on the database servers. Sqlmap utilizes a command-line interface and is compatible with platforms like Apple, Linux, Mac, and Windows.
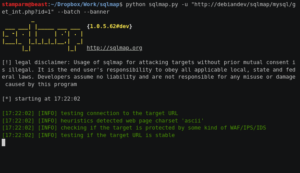
Sqlmap Penetration Testing Tool.
15. John The Ripper.
John the Ripper is made to operate in the majority of the environments nevertheless, it was created mainly for Unix systems. This one of the fastest pen-testing tools includes password hash code and strength checking code to let you incorporate it into your system or software application, making it a distinct alternative.
This tool can be availed free of charge or else you can also opt for its pro version for some extra functions.
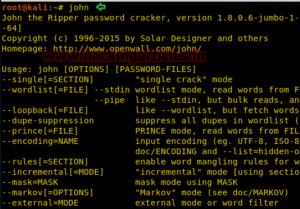
John Ripper Password Cracker.
16. Burp Suite.
Burp Suite is a cost effective pen testing tool that has marked a standard in the world of testing. This awesome tool intercepts proxy, web application scanning, crawling material and functionality, etc it can be used with Linux, Windows, and macOS.

Burp Suite Application Security Testing.
Conclusion.
There is nothing beyond preserving correct security while identifying concrete hazards and damage that can be caused to your system by criminal hackers. However do not you worry as, with the implementation of the above-given tools, you will have the ability to keep a keen eye on such activities while getting prompt informed on the same to take additional action.